With a strong authentication mechanism, more than 9 out of 10 attacks can be defended against. This is now widely known and undisputed. Every day, we access systems that require a username and password. The high-profile hacks and data breaches of the past few years have opened the eyes of many to how vulnerable such logins can be.
“Advanced authentication” or multi-factor authentication is just about mandatory these days. But there are a few things to keep in mind – regardless of the solution.
How well does multi-factor authentication (MFA) work?
MFA is simply a login process that requires users to not merely enter their credentials but to present two or more proofs before they can log into an account.
The obvious benefit of multi-factor authentication is increased security by adding additional layers of protection, which means it becomes more difficult for a potential intruder to gain access to accounts and data.
This has been proven to have a huge effect on security. But MFA is not a magic bullet. In addition to the undeniable benefits, there are some challenges to consider when implementing multi-factor authentication.
Problem 1: Adoption is generally low
Multi-factor authentication can be a hurdle. For some users, possibly even one too many. Even though many workers are familiar with MFA, less technically savvy employees may find it challenging to log in.
A big reason for this is that passwords are still required for most logins. Users then have to manage not only the password but also the additional layers of security. These can be apps, SMS messages, code cards, USB sticks, PIN devices, security questions, and more.
![]()
![]() Apps
Apps
![]() SMS
SMS
![]() Code cards
Code cards
![]() USB sticks
USB sticks
![]() PIN devices
PIN devices
![]() Security questions
Security questions
and more.
As a result, people are adopting strategies to simplify their lives. One study shows that an estimated 55% of Internet users use the same password for all their accounts, which only further emphasizes the need for MFA. As cybersecurity will remain essential for businesses in the future, educating employees on the importance of security and proper training on how to use MFA will have to take a substantial place.
Problem 2: Access codes can be stolen
Meanwhile, attackers are busy finding new ways to breach these new layers of protection. A recently released penetration testing tool can automate phishing attacks fairly easily, according to ZDNet, and hack even MFA-secured logins through stolen access codes – as long as they’re only double-protected using simpler methods like security questions or SMS codes. So it’s also important to opt for strong secondary (and tertiary) layers of security where access codes cannot be stolen such as biometrics.
Problem 3: Jumping from one account to the next
Another problem is that a hacked account can be a goldmine to compromise other accounts. A customer account at an unknown, small tea store seems unimportant?
Beware. Once an attacker has penetrated an account, no matter how unimportant it seems, they are often able to extrapolate the “seed” or secret key of a TOTP (time-based one-time password) and use it to gain access to higher value targets like bank accounts.
The only thing that can help here is good password hygiene (which means using a different, secure password everywhere) and strong MFA, preferably using AI-assisted dynamic factors that are context-, time-, location- or process-based. Example: If you are currently in Zurich with your smartphone, it is unlikely that you will log into your e-banking in Singapore at the same time.
Problem 4: Multi-factor authentication – just roll it out quickly and well?
From an IT perspective, most authentication mechanisms may be similar. Whether it’s SMS, an extra app, or a hardware token on a keychain. But users usually see it differently. Regardless of the industry, for a seamless transition to MFA, IT leaders need to ensure that affected users are heard first and then also forewarned and prepared for the change. Most of the problems associated with MFA are due to a lack of user awareness and acceptance!
We have already mentioned the importance of information and education above. Security needs a cultural slot in the company and it is not just there, it has to be prepared. This is laborious and time-consuming and has nothing to do with IT. That’s why most people in charge don’t do it or do it only sullenly. However, it cannot be emphasized enough how dangerous this is. It is a fact that this is precisely what creates a significant security risk.
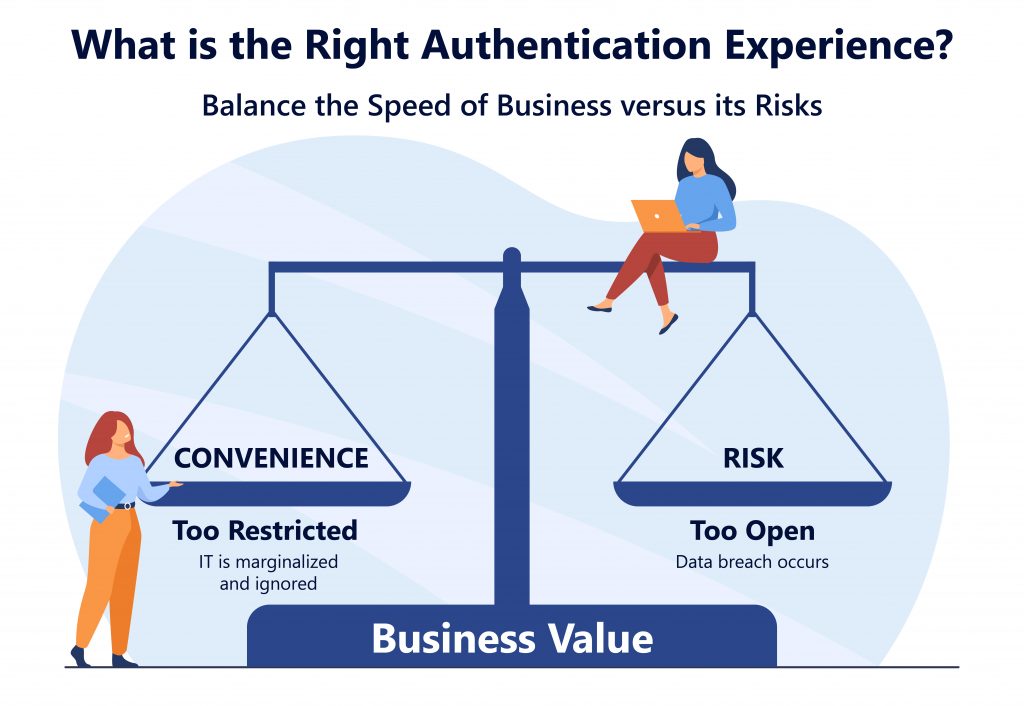
MFA is not the goal, but the way
Authentication is expected to enhance security without being disruptive. It is not the goal, not the gain, but rather a mortgage. Poor implementation means frequent errors, many IT tickets and password reset requests, long waiting times, and the potential exposure of sensitive information.
It has been found to be especially important to consider user workflow. MFA must integrate seamlessly into the workflow. The central element here is single sign-on: the user centrally authenticates once and in the background, his credentials are federated to all important target systems, so that he can work with all systems without having to log on individually. If this is ensured, acceptance of the one-time central logon increases enormously, even if it is relatively cumbersome because it consists of several factors.
Moreover, if you succeed in eliminating the password, you are not only assured of acceptance but in all likelihood even the thanks of the employees. And yes, with a flexible solution, this is possible! And it makes it even more secure.
The challenges are real, but implementing advanced authentication is doable. With the right approach, success is all but assured. By doing so, you enable your employees to better understand their responsibilities when it comes to the security and protection of your data and assets
💡 Sources:
ITProPortal “The challenges of multi-factor authentication in your security program”